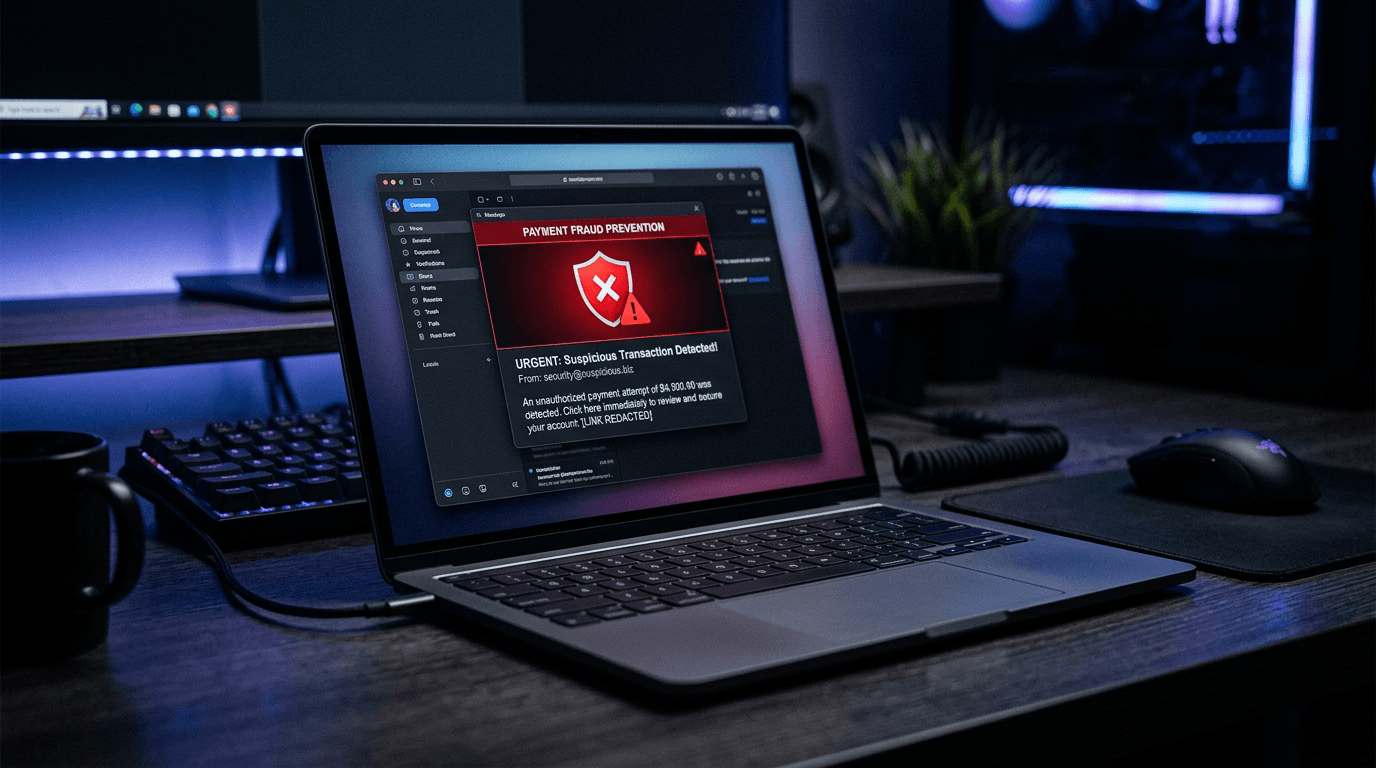
A hotel controller in Miami processes an urgent wire transfer after receiving an email from the CEO requesting immediate payment to a new vendor. The email looks legitimate. The request makes sense. But the email was spoofed, the vendor doesn't exist, and $47,000 is gone. This is not a hypothetical scenario. Business Email Compromise (BEC) attacks cost U.S. businesses over $2.9 billion in 2025, and hospitality is a prime target.
Restaurants, hotels, venues, and event production companies are particularly vulnerable to payment fraud for reasons that are structural to the industry: high vendor volume, frequent one-time payments, cash-intensive operations, time pressure around events, and decentralized decision-making across locations. The good news is that most payment fraud in hospitality is preventable with the right controls, workflows, and awareness.
This guide covers the most common fraud schemes targeting hospitality businesses, the red flags to watch for, and the practical controls that stop fraud before money leaves your account.
Common Fraud Schemes in Hospitality
Understanding how fraud happens is the first step in preventing it. These are the schemes we see most frequently in the hospitality industry.
Fake Invoice Fraud
How it works: A fraudster sends a legitimate-looking invoice to your AP department for a product or service that was never delivered. The invoice uses a real vendor name, references plausible purchase order numbers, and is for an amount that falls below your typical review threshold.
Why hospitality is vulnerable: High invoice volume and frequent one-time vendor relationships make it harder to catch fakes. A 10-location restaurant group processing 500+ invoices per month can't manually verify every one. A $380 invoice from "Metro Pest Control" for a quarterly service call looks routine, even if you've never actually contracted with that company.
Real-world pattern: Fraudsters often send invoices to multiple locations within the same group, betting that at least one location will process the payment without verifying the service was performed. A fake invoice for $200 sent to 15 locations nets $3,000 with minimal effort.
Business Email Compromise (BEC)
How it works: An attacker compromises or spoofs an email account belonging to a company executive, vendor, or trusted partner. They use this access to send payment instructions that appear legitimate.
Common BEC variations in hospitality:
- CEO impersonation: "I need you to wire $25,000 to this vendor today. I'm in a meeting and can't talk, but this is urgent." The email comes from an address that looks like the CEO's (one character off, or a lookalike domain).
- Vendor email compromise: A real vendor's email account is hacked. The attacker sends an email from the vendor's actual address saying, "Our banking information has changed. Please update our account details for future payments." The new account belongs to the attacker.
- Attorney impersonation: Someone claiming to be from your business's law firm requests an urgent payment related to a confidential matter, pressuring you not to verify through normal channels.
Why hospitality is vulnerable: Fast-paced operations create a culture of urgency. When the catering director says a vendor needs to be paid today for an event tomorrow, AP teams are conditioned to move quickly. Fraudsters exploit this urgency.
Vendor Impersonation
How it works: A fraudster creates a business that mimics a legitimate vendor. They might register a domain similar to a known vendor (sysco-foods.net instead of sysco.com), create professional-looking invoices, and send them to your AP department.
Alternatively, they contact your business claiming to be from an existing vendor and request an update to banking information. The "updated" bank account belongs to the fraudster. Your next legitimate payment to that vendor goes to the wrong account.
Why hospitality is vulnerable: Large vendor lists and staff turnover mean that AP clerks may not personally know every vendor. A convincing impersonation of a vendor your business has used once or twice can easily go undetected.
Check Fraud
How it works: Physical checks are intercepted (often from mailboxes), altered (payee name or amount changed), or counterfeited. Check washing, where the ink is chemically removed and the check rewritten, is the most common method.
Why hospitality is vulnerable: Despite the availability of electronic payments, many hospitality businesses still pay 40-60% of vendors by check. Each check that enters the mail system is a potential fraud target. For a comparison of payment security across methods, see our ACH vs. check analysis.
Internal Fraud
How it works: An employee with AP access creates fictitious vendors, submits fraudulent invoices, or diverts payments to personal accounts. This can also involve an employee colluding with a real vendor to inflate invoices and split the difference.
Why hospitality is vulnerable: Single-person AP departments are common in independent restaurants and small hotel groups. Without segregation of duties, one person may have the ability to create vendors, approve invoices, and process payments with no oversight.
Red Flags to Watch For
Train your AP team, location managers, and anyone involved in vendor payments to recognize these warning signs.
Invoice Red Flags
- Round-number invoices ($500.00, $1,000.00). Legitimate invoices for services rendered almost always have odd amounts.
- Missing or vague descriptions. "Consulting services - March" instead of specific deliverables and dates.
- No purchase order reference for invoices that should match a PO.
- Vendor contact information that doesn't match records. Phone number, email, or address is different from what's in your vendor master.
- Invoices just below your approval threshold. Fraudsters research common thresholds and price their fake invoices accordingly.
- Duplicate invoice numbers or sequential invoice numbers from a vendor who typically has gaps.
- First-time invoices from vendors you don't recognize, especially if no one in the requesting department can confirm the engagement.
Communication Red Flags
- Urgency and pressure. "This needs to be paid today" with no prior context.
- Requests to bypass normal processes. "Don't bother verifying, just process it."
- Communication channel changes. A vendor who always calls now only communicates by email, or vice versa.
- Requests for confidentiality. "Don't mention this to anyone else."
- Changes to banking information via email without phone verification.
- Emails with slight domain variations. "vendor@sysco-inc.com" instead of "vendor@sysco.com."
Behavioral Red Flags
- An employee who never takes vacation (may be hiding ongoing fraud that would be discovered in their absence).
- An AP team member who insists on handling specific vendors exclusively.
- Vendors who are unusually accommodating about payment timing or terms (because they're not actually delivering anything).
- Lifestyle changes in employees with access to financial systems that don't match their compensation.
Building Fraud Prevention Controls
Effective fraud prevention combines technical controls, process controls, and cultural awareness.
Dual-Approval Workflows
The single most effective fraud prevention control: require two independent approvals for payments above a defined threshold.
Key principles:
- Separation of duties: The person who creates the vendor record should not be the person who approves payments to that vendor.
- No self-approval: No one should approve their own expenses or payments to vendors they personally engaged.
- Independent verification: Approvers should independently verify the legitimacy of the payment, not rubber-stamp the first approver's decision.
Vendor Verification Procedures
Before activating a new vendor or processing a banking change:
- Verify independently. Call the vendor at a phone number you look up independently (not the number on the invoice or email requesting the change). Confirm the payment request or banking update.
- Check registration. For new vendors, verify their business registration with the state secretary of state's office. Confirm they're a real, registered entity.
- Validate W-9 information. Run TIN verification through the IRS TIN matching program before processing the first payment.
- Confirm with the requester. If a department head engaged the vendor, confirm the engagement and expected costs directly (in person or by phone, not by replying to the potentially compromised email).
For a comprehensive vendor onboarding process that builds verification into the workflow, see our onboarding guide.
Banking Change Controls
Banking information changes are one of the highest-risk transactions in AP. A single successful banking redirect can cost tens of thousands of dollars. Implement these controls:
- Mandatory phone verification. Any request to change vendor banking must be verified by phone with the vendor, using a number from your existing records (not the number provided in the change request).
- Waiting period. Implement a 48-72 hour hold on banking changes before the first payment to the new account. This gives you time to detect and reverse a fraudulent change.
- Dual authorization. Require two people to approve any banking information change.
- Test payment. Send a small test payment ($1-$5) to the new account and have the vendor confirm receipt before sending a full payment.
Email Security
Since BEC is one of the most costly fraud vectors:
- Enable multi-factor authentication (MFA) on all email accounts, especially those with financial authority.
- Implement email authentication protocols (SPF, DKIM, DMARC) to reduce spoofing.
- Train staff to verify requests received by email through a second channel (phone call, in-person confirmation).
- Never process payment changes or urgent wire requests based solely on email instructions.
- Flag external emails with a banner indicating they originated outside your organization.
Ready to simplify your AP workflow?
Get early access to Cleo Pay and see how we help hospitality teams save hours every week.
Check Security Measures
If you still use checks (and you should be migrating to ACH where possible):
- Use positive pay. This bank service matches checks presented for payment against a list of checks you've issued. Any check that doesn't match is flagged before it's paid.
- Secure check stock. Store blank checks in a locked location with limited access. Track check numbers and investigate gaps.
- Use security features. Tamper-evident paper, watermarks, micro-printing, and chemical-sensitive ink make checks harder to alter.
- Reconcile promptly. Review bank statements and cleared checks within 48 hours. The faster you spot unauthorized activity, the more likely you can recover funds.
- Minimize check usage. Every check eliminated is a fraud vector closed. Target moving your top 20 check-paid vendors to ACH within the next 90 days.
Internal Controls
Protect against insider threats without creating a culture of distrust:
- Segregation of duties. Separate vendor creation, invoice approval, and payment execution across different people. In small teams where this isn't fully possible, implement compensating controls (e.g., the owner reviews all new vendor setups monthly).
- Regular vendor master audits. Quarterly, review your vendor list for inactive vendors, duplicate entries, and vendors that no one recognizes. Deactivate any vendor with no legitimate activity in the past 6 months.
- Exception reporting. Generate reports for unusual patterns: payments to new vendors, payments just below approval thresholds, vendors with recent banking changes, payments to vendors with P.O. box addresses.
- Mandatory vacations. Require AP staff to take at least one continuous week of vacation annually. Fraud that depends on a single person's involvement often surfaces when that person is absent.
- Anonymous reporting. Provide a way for employees to report suspicious activity without fear of retaliation.
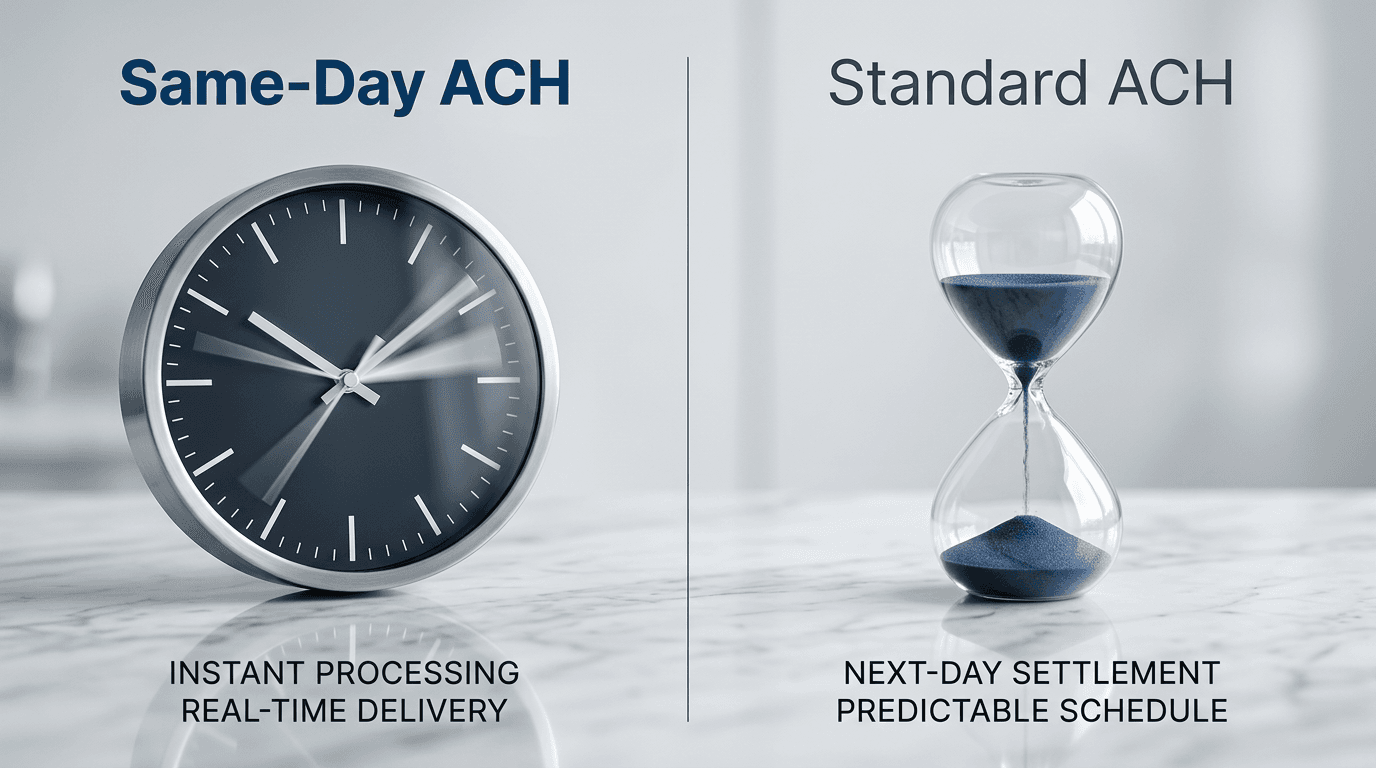
ACH vs. Check: A Security Comparison
The security differences between payment methods are significant and often underappreciated.
The comparison is stark. ACH eliminates the physical attack vectors (interception, alteration, counterfeiting) that account for the majority of check fraud losses. It also provides faster detection through electronic monitoring and higher recovery rates because electronic transactions can be traced and sometimes reversed.
This doesn't mean ACH is immune to fraud. Unauthorized ACH debits and fraudulent vendor banking changes are real risks. But the available controls (dual authorization, banking change verification, positive pay equivalents) are stronger and more effective than the controls available for paper checks.
Fraud Prevention Checklist
Use this checklist to assess and strengthen your fraud prevention posture. Score yourself on each item: fully implemented, partially implemented, or not implemented.
Process Controls
- Dual-approval workflow for payments above threshold
- Segregation of duties between vendor creation, invoice approval, and payment execution
- Mandatory phone verification for vendor banking changes
- New vendor verification process (TIN matching, business registration check)
- Regular vendor master audits (quarterly minimum)
- Exception reporting for unusual payment patterns
- Invoice matching against POs and receiving records
Technical Controls
- Multi-factor authentication on all email accounts
- Email authentication (SPF, DKIM, DMARC) implemented
- External email flagging enabled
- Positive pay for check payments
- Secure check stock storage with access logging
- Automated duplicate payment detection
- Bank statement reconciliation within 48 hours
Cultural Controls
- Annual fraud awareness training for AP staff
- Annual fraud awareness training for managers who approve payments
- BEC simulation exercises (test phishing emails)
- Anonymous reporting channel available
- Mandatory vacation policy for AP staff
- Clear escalation path for suspicious activity
- Documented fraud response plan
Vendor Management Controls
- W-9 collection before first payment (see our guide)
- TIN verification for all vendors
- Insurance verification for on-premises vendors
- Vendor onboarding process standardized across locations
- Banking changes require dual authorization and phone verification
- Vendor deactivation process for inactive relationships
- Regular review of vendor contact information against independent sources
What to Do When You Suspect Fraud
Speed matters. If you suspect a fraudulent payment has been processed:
Immediate Actions (First 2 Hours)
- Contact your bank immediately. Request a hold or reversal on the payment. For ACH, returns must be initiated within 2 business days. For wires, contact your bank's fraud department; recovery is possible but time-sensitive.
- Preserve evidence. Do not delete emails, modify records, or contact the suspected fraudster. Save everything.
- Lock accounts. If you suspect email compromise, immediately change passwords and enable MFA on affected accounts.
- Document the timeline. Record when the fraudulent request was received, when the payment was processed, and when the fraud was discovered.
Next 24 Hours
- File a report with IC3 (Internet Crime Complaint Center at ic3.gov) if the fraud involved email compromise or internet-based schemes.
- File a police report with local law enforcement.
- Notify your insurance carrier. If you have cyber insurance or crime insurance, report the incident per your policy requirements.
- Conduct an internal review. How did the fraud succeed? Which controls failed? Were existing procedures followed?
Within One Week
- Implement immediate control improvements based on the review findings.
- Communicate with affected parties. If vendor data was compromised, notify affected vendors.
- Retrain staff on the specific fraud technique that was used.
How Cleo Pay Strengthens Fraud Prevention
Cleo Pay builds fraud prevention into the payment workflow rather than adding it as an afterthought.
Vendor verification at onboarding. Every vendor goes through TIN verification and banking validation before they're activated. Fraudulent vendors are caught before the first payment.
Dual-approval workflows. Configure approval chains based on payment amount, vendor type, and location. No single person can create a vendor and pay them without independent approval.
Banking change alerts. When vendor banking information is updated, Cleo Pay flags the change, requires dual authorization, and provides a verification workflow before payments route to the new account.
Duplicate payment detection. The platform automatically flags potential duplicate invoices based on vendor, amount, date, and invoice number patterns.
Complete audit trail. Every action (vendor creation, invoice approval, payment execution, banking changes) is logged with who did it, when, and from what device. This trail is invaluable for both fraud detection and post-incident investigation.
ACH-first payments. By defaulting to ACH over checks, Cleo Pay eliminates the physical fraud vectors that account for the majority of payment fraud in hospitality.
For hospitality businesses serious about protecting their payment operations, start with a demo to see how these controls work in practice.
The Cost of Doing Nothing
Payment fraud in hospitality is not a matter of "if" but "when." The median fraud loss for small-to-mid-size businesses is $150,000 per incident, according to the Association of Certified Fraud Examiners. For a restaurant group operating on 8-12% net margins, recovering from a $150,000 fraud loss requires $1.25-$1.88 million in additional revenue.
The controls described in this guide cost a fraction of a single fraud incident to implement. Most require process changes rather than technology investments. And the ones that do require technology, like AP automation with built-in fraud controls, pay for themselves through operational savings independent of fraud prevention.
Start with the checklist. Identify your gaps. Close them before they're exploited.